OpenVPN FAQs
Download Links
OpenVPN supports most operating systems. Download the appropriate client from the links below.
Deployment instructions are here: Configure and deploy OpenVPN Clients for remote users
Microsoft Windows
You can download the Windows client from here: https://openvpn.net/community-downloads/.
Apple macOS
You can download the macOS client here: https://openvpn.net/client-connect-vpn-for-mac-os/
Linux
A Linux client is available here: https://openvpn.net/openvpn-client-for-linux/
Chrome OS
Steps to install OpenVPN on Chrome OS devices:
https://support.untangle.com/hc/en-us/articles/207304818-Deploy-the-OpenVPN-Client-to-a-Chromebook
iOS Mobile Devices

For iPhones, we suggest OpenVPN Connect available on iTunes https://itunes.apple.com/us/app/openvpn-connect/id590379981?mt=8
- Install OpenVPN Connect app on your iPhone or iPad.
- Login to the NG Firewall server, download the client config file by selecting "client configuration zip for other OSs".
- Unzip the config file.
- Open iTunes and select the .ovpn, .crt, and .key files from the config zip to add to the app on your iPhone or iPad.

Android Mobile Devices
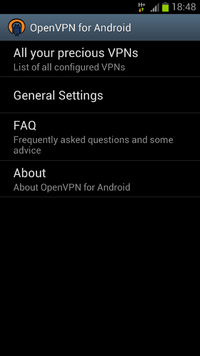
You can download the OpenVPN Connect client app from the Google Play Store: https://play.google.com/store/apps/details?id=net.openvpn.openvpn
Other FAQs
Is there a way to set up a password for the OpenVPN users?
Yes, if you right-click on the OpenVPN icon on the client's PC there is an option for a password. Please note this password is only used when launching the client.
How can I restrict access to certain OpenVPN users?
By default, OpenVPN users can connect to any machine that the NG Firewall can connect to. However, routes are pushed to all the "Exported" network automatically. Be aware that nothing prevents remote users who have administrator access to their machines from adding routes manually.
If restricting access to OpenVPN users is a concern, Firewall rules or Filter Rules can be used. In the Firewall app, the easiest way is to create a block rule blocking traffic when Source Interface == OpenVPN. Above that rule, create rules to allow traffic when Username is the OpenVPN user you want to allow to the desired locations. In this scenario OpenVPN traffic will be blocked into your network except for explicitly allowed traffic.
Using rules you can limit access to certain resources to only the desired remote users.
Can I create site-to-site tunnels with non-NG Firewall devices?
When using OpenVPN for site-to-site tunnels we only support using other NG Firewall endpoints. Some users have had success with DD-WRT and Tomato, but this is not supported by the Support team. If you need to connect a VPN tunnel to an endpoint that isn't another Arista ETM device, we recommend using IPsec VPN.
I'm using site-to-site and my software clients can only talk to the main server. Why?
If you have both software clients on the road and site-to-site tunnels, the software clients will only be able to see your main site by default. To allow them to transit the tunnel(s) to other sites, simply add the VPN Address Pool to the Exported Hosts and Networks. After this is done, software clients will be able to reach all exported sites.
How can I allow software clients to resolve DNS over the tunnel?
To allow DNS resolution for remote clients you'll need to modify some OpenVPN settings - if NG Firewall is doing DNS resolution on your network, simply check Push DNS in OpenVPN Settings > Server > Groups > Group Name for any groups you want to push DNS settings to. Configure the DNS settings you would like pushed to the remote clients. You may need to use the FQDN when accessing resources across the tunnel.
Clients are getting disconnected after 60 seconds. Why?
Did you share the same client config between multiple machines? If both are running simultaneously, they will conflict: when the second connects the first is disconnected. After 60 seconds, the first will reconnect and disconnect the second. This repeats endlessly. Do not share the same client config with multiple machines.
I'm setting up a new client and can't connect. Why?
Make sure that the IP that the client is connecting to is the public IP of the server, or that the traffic to that IP on port 1194 is being forwarded to your server. Also make sure you are testing from the outside. By default the Access Rules block OpenVPN clients from connecting to a server from one of its own LANs. This is to prevent clients from losing connectivity while on the local network because of a routing loop.