Bypass Rules
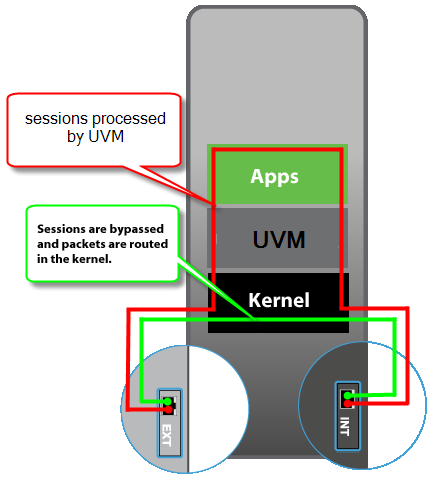
NG Firewall's applications run in what we call the "Untangle VM" - the Untangle Virtual Machine. During this process, both UDP and TCP streams are endpointed and their streams are reconstructed at layer 7 (the application layer). The data stream then flows through the applications, and if passed eventually the data is put back into new packets and sent on its way.
Unlike most proxy firewalls, by default NG Firewall processes almost all ports of both UDP and TCP at the application layer. In some cases, it may be ideal to "bypass" traffic so that it is not subject to scanning. As shown in the image on the right bypassed traffic will skip all of the NG Firewall VM layer 7 processing and all the applications.
Sometimes it is ideal to bypass traffic for performance reasons. It can either be traffic that you are not interested in scanning and wish to save server resources, or traffic that is extremely sensitive to scanning, like VoIP.
Sometimes it is also necessary to bypass traffic that the application layer processing interferes with.
Bypassed sessions are still routed, NATd, and filtered identically to all other sessions, as defined by your network configuration. The only difference is that bypassed sessions are not processed at layer 7 so their traffic "bypasses" the applications.
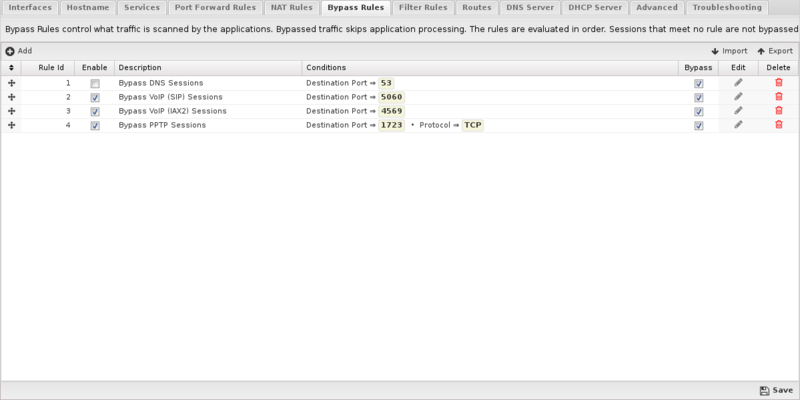
Bypass Rules
Bypass Rules work like other Rules. They are evaluated in order. The action from the first matching rule is taken.
As an example, lets say you have a backup server at 1.2.3.4 and you don't want traffic to that backup server scanned or interfered with in anyway. To bypass it create a rule with Destination Address = 1.2.3.4 and action = "Bypass"

Bypass Rules contain several components.
- Enable
- If checked, the rule is enabled. If unchecked the rule has no effect and is disabled.
- Description
- A description of this rule. This is just for documentation.
- Conditions
- The conditions describing which sessions will match. As documented in Rules#Condition_List
- Action
- Bypass or Process. Bypass means the traffic will be bypassed. Process means the traffic will be processed by the UVM and the apps.
Like all rules, the Bypass rules are evaluated in order. The session will be processed or bypassed according to the first matching rule. If no bypass rule matches, the session will be processed.
Common Uses
There are several scenarios which it usually makes sense to bypass traffic.
On large networks with servers that might be very busy it usually makes sense to bypass traffic that need not be scanned. This all depends on why you are using NG Firewall on your network.
Often I check in Reports under "System" and look at the "Top Destination Ports." Occasionally you'll see some bizarre port with millions of sessions, like syslog. Often these ports can be bypassed if you don't care to scan them.
Often it makes sense to bypass port 53 from your internal DNS server so you can guarantee that NG Firewall will not interfere with your DNS server's resolution process. This is critical if NG Firewall is using this server for DNS resolution itself.
If you are using NG Firewall for just Web Filter then you can basically bypass all of UDP and save lots of processing time, although obviously this isn't a good idea if you are using Bandwidth Control as then it would not be able to shape UDP.
Bypassing can sometimes be useful for troubleshooting. If you are having issue with some traffic you can bypass it to see if it helps. If it does help then revert back to processing and disable the apps one at a time to see if its one of the applications interfering with the traffic in question.