Application Control Lite
About Application Control Lite
Application Control Lite scans sessions for the specified signatures and will log and/or block sessions based on their content. Many applications can be hard to block based on port as modern applications will find and use open ports automatically. Application Control Lite provides a basic functionality to block sessions based on the content (data) in the session.
Settings
This section reviews the different settings and configuration options available for Application Control Lite.
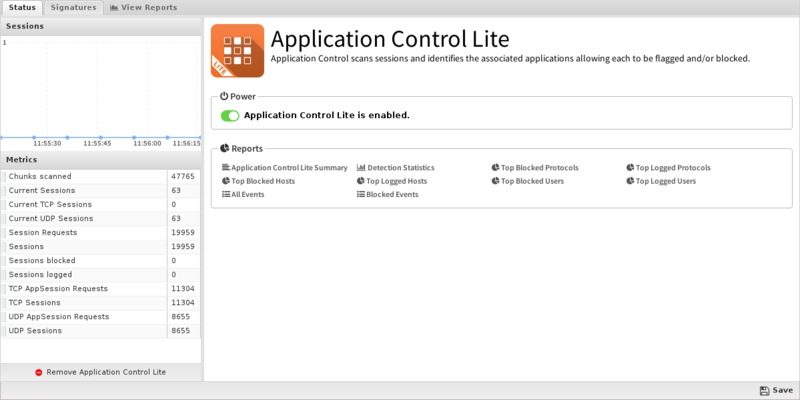
Status
The Status tab will show you current information on signatures Available, Logged and Blocked.
Signatures
The Signatures tab shows the the list of current signatures. Signatures are regular expressions that are written to match know protocols as accurately as possible. New custom signatures can be designed to match certain applications or sessions, or signatures can often be found for many existing protocols here.
As the early data in each session goes from the server to the client and the client to the server, it is stored in a buffer. As each chunk of data arrives the data is evaluated against any enabled signatures. If the signature is checked "log" then the session will be tagged and logged as having matched the specified signature. If the signature is checked "block" it will be logged and the session will immediately be closed.
Writing custom signatures can be dangerous and difficult. Usually one of several outcomes will happen when writing a block signature:
- It will not match anything. In this case, the signature needs to be fixed.
- It will block the desired protocol/application and nothing else. This is ideal.
- It will only partially block the protocol. Many multi-session protocols only have some sessions identified. This can have varying effects depending on the application.
- It will block the protocol and block other things too (false positives). This can cause major problems with the network.
- It will block the protocol and the application will adapt and use an alternative protocol to communicate. Many applications will try alternative techniques to avoid blocking.
As such great care and expertise is involved in writing signatures to achieve the desired effect.
NOTE: Application Control Lite, while powerful, can be difficult, time consuming, and dangerous to configure correctly. Application Control is recommended for most users as it comes preloaded with hundreds of maintained and current behavioral signatures and a commercial third-party application identification engine.
WARNING: In previous and old versions of Untangle there was a default signature set. However, enabling block on some of the default signatures caused false positives and blocked legitimate network traffic. Despite big warnings in the user interface and help documentation, we found users often misconfigured Application Control Lite anyway and experienced network problems as a result. To avoid this issue there are now no default signatures. If you have read this warning and understand that misconfiguring Application Control Lite will cause major network connectivity issues, then you can download the original list of signatures here and import them into Signatures.
Reports
The Reports tab provides a view of all reports and events for all traffic handled by Application Control Lite.
Reports
This applications reports can be accessed via the Reports tab at the top or the Reports tab within the settings. All pre-defined reports will be listed along with any custom reports that have been created.
Reports can be searched and further defined using the time selectors and the Conditions window at the bottom of the page. The data used in the report can be obtained on the Current Data window on the right.
Pre-defined report queries: {{#section:All_Reports|'Application Control Lite'}}
The tables queried to render these reports:
Related Topics
Application Control Lite FAQs
What's the difference between Application Control and Application Control Lite?
Application Control is based on a commercial third-party application identification engine. It support many many more applications, is more accurate, faster, and is better maintained. False positives are very rare.
Application Control Lite runs simple regular expression signatures against the datastream. If a signature matches the traffic, the chosen action is taken for that particular signature. These signatures are not exact matches and can have false positives.
I've already installed the Firewall. Isn't Application Control Lite redundant?
The Firewall application works to block traffic by IP addresses and/or ports. For well-behaved applications (such as legitimate web and email servers) the port can be used to identify the protocol. Less than legitimate applications may use different ports, or malicious users may deliberately use unwanted services on obscure ports. Application Control Lite scans all traffic, looking for a match even if traffic was not transported across the expected port for that protocol.
How do I add a protocol to Application Control Lite?
To add a protocol you must provide Application Control Lite the protocol's signature. To determine the signature, you must analyze the packets, and this process can be tricky. More information is available at the L-7 Filter site. Please be aware that not all protocols can be blocked because some protocol designers detect and avoid blocking with encryption (for example, Skype).
What happens if I set a protocol to block?
A few things could happen:
- It will not detect anything.
- It will block the protocol completely.
- It will only partially block the protocol (many multi-session protocols only have some sessions identified).
- It will block the protocol and block other things too (false positives).
- It will block the protocol and the application will adapt and use an alternative protocol to communicate.
Please be aware of these possible results and be sure to do some testing when using or adding specific rules.
I want to block a file sharing protocol for some of my users but not all. How can I do this with Application Control Lite?
Application Control Lite cannot filter just for some machines and not others by itself - you can use Policy Manager to create a new rack, send specific users to the new rack, then configure Application Control Lite in that rack as you see fit for those users.
